Corporate processes

A security audit is performed through the analysis and management of systems with the goal of identifying, categorizing and describing potential vulnerabilities within the organization: workstations, networks and WiFi, infrastructure and business applications.
Once the audit is performed, corrective and preventive measures must be implemented by following a continuing risk reduction process that allows for greater security for the business’ systems.
We at mrHouston work on corporate processes adaptation through several stages.
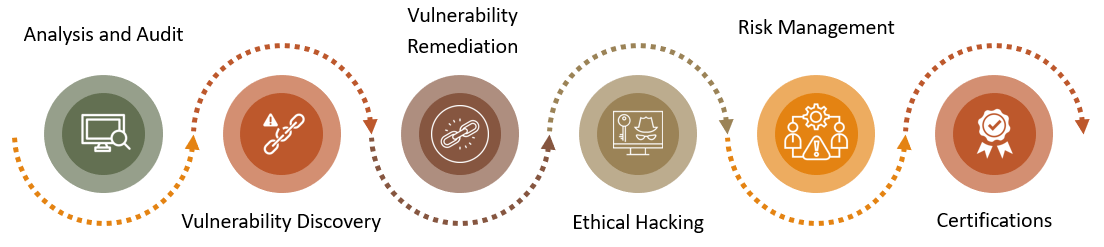
ANALYSIS AND AUDIT
- Security settings audit
- Identification of malware in file containers
- Applications audit
- Code analysis
- IP reputation audit
VULNERABILITY DISCOVERY
- Compromised and affected systems and applications
- Outdated systems
- Remediation
- What does it entail (impact)?
- Correction services
ETHICAL HACKING
BLACK BOX
Access to very little data with no collaboration from the business’ IT team.
WHITE BOX
Close collaboration with the business’ IT team and significant access to its data. “Red & Blue Team”
INTERNAL AND EXTERNAL PENETRATION TEST
- Networks and infrastructure
- WiFi
- Website
- Email phishing
SOCIAL ENGINEERING
Planned attack carried out by introducing malware through the weakest human link in the organization.
RISK MANAGEMENT, CERTIFICATIONS
INFORMATION SECURITY- ISO 27001
Allows for the planning, execution, verification and improvement of a set of controls, technical measures, procedures and organizational frameworks that will enable businesses to reduce risk and, above all, provide them with a security process management scheme
BUSINESS CONTINUITY - ISO 22301
Guarantees the alignment of IT services with the company’s corporate governance requirements and strategy.
IT SERVICES - ISO 20000
Any business, no matter its size, will reduce the risk of suffering a potentially damaging incident and, if it occurs, the business will be prepared to respond appropriately and drastically reduce any potential damage resulting from the incident.
Improves the business’ organization
Dramatically reduces risks

Allows for dashboards

Grants access to new markets and clients
Demonstrates good practices
Adequate management of unexpected events

Hundreds of audit controls
Reduces resource consumption




